The first week of classes went well for this course. One of the questions I love ask students after I go over the course schedule is “what would they like me to present on in addition to what I planned?”.
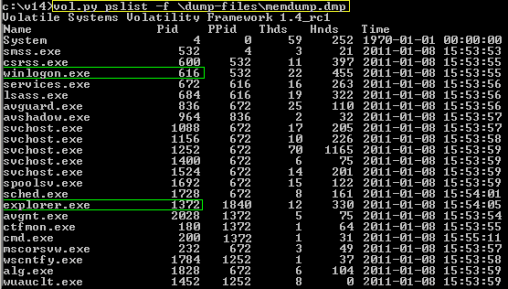
The overwhelming response from students (mostly junior / senior – Computer Forensic / Computer Networking and Security) was Malware Analysis. Typically I present Malware Analysis in our FOR430 Advanced Topics course – we spend about 6 weeks delving into the basics through some very entry level static/dynamic analysis techniques.
So malware analysis – it’s hard. it’s not something you can completely learn in one course. Take it from Patrick Olsen’s blog post review of the highly regarded Sans FOR610 course “Reverse-Engineering Malware: Malware Analysis Tools and Techniques”. While this couse is lead by an expert in the field, typically Lenny Zeltser, and I’ve only heard amazing things about it, it takes a lot of technical preparation (in my opinion having some considerable computer science background for the static analysis and OS internals/network analysis for dynamic analysis) to be ready to take the course. It also requires you to be committed to the specific area of study. I’ve always said, Digital Forensic Incident Response (DFIR) teams are like a puzzle, everyone will have their niche expertise, but everyone will need to work together during an incident to reach success.
 |
| Digital Forensic/Incident Response professionals are apart of a larger collective of experts. We need everyone to work together to fight evil. |
That said, due overwhelming interest from the students, in this Operating System Forensics course we will cover some of the basic static and dynamic analysis techniques. However, students will need to master all of my planned content including file system analysis/operating system analysis. Also, as an aside, malware analysis is the buzzword – what professionals are actually doing is a behavioral analysis of code/software. We focus on “malware” because that’s whats negatively impacting our networks/computers.






.jpg)
