This is the first post for the 2012 Fall Operating System Forensics course at Champlain College. This course is focused on teaching students how to extract and analyze information from some of the most commonly seen operating systems.
We will explore aspects from basic analysis all the way through some of the most leading edge analysis methodologies that will help students prove if a particular computer was involved in the cybercrime. This course is very much “hands on” and students are expected to spend a considerable amount of time working alone and in teams to complete their projects.In this course I focus on students being able to complete the technical aspects, but also able to communicate the technical results verbally/in reports. By the end of this course students will be able to conduct an analysis on computers involving common crimes (theft of intellectual property, inappropriate use of systems, data destruction, AUP violation etc) and write a report /testify to the work that should stand up in a court of law.
 |
| http://www.h-online.com/security/features/CSI-Internet-A-trip-into-RAM-1339479.html |
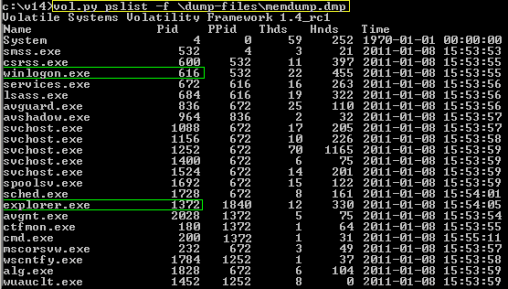
We will be using many open source/freeware/commercial tools to analyze evidence. We focus very much on students not blindly relying on the tools, but understanding what’s happening within the evidence regardless of which tool is being used. That said, we do teach students the very same tools that are being used by major consulting / government agencies including but not limited to EnCase 6.x/7.x, FTK 4.x, regripper, volatility and many,many more. We will have access to virtual machines that we will use to build operating systems, create “evidence” and examine that evidence. Students will also explore many hands on investigation scenarios that will help them strengthen their skills. Students leave this class feeling comfortable conducting digital forensic exams on digital devices.
.jpg) |
| To read full article please visit http://www.guidancesoftware.com/DocumentRegistration.aspx?did=1000018034 |
At the same time this course is offered, I will be teaching a graduate course in Operating System Analysis – if we have time at the end of this class I want to intergrate a lecture or two on some of the advanced topics discussed in the graduate course.